SynopsisData security is a major concern for companies across sectors in the era of work from home. While employers are using surveillance software to keep a close watch on how their employees use company hardware, they should take measures to ensure that it doesn’t amount to intrusion of privacy.
A few days back, one of our colleagues received a strange message from the corporate communications head of a Delhi-based company. The gist of the message was simple. It said he had come to know that our colleague was pursuing the company’s employees on LinkedIn with queries for a story.
This, he added, was not as per the protocol since nobody in the company, other than the communications head, was allowed to speak to the media.
My colleague came to us with a simple question. How did the corporate communication head come to know of the LinkedIn messages? There were two options. The first was that employees reported the attempts to connect by our colleague. That could well have been the case here, as well. But a second, more intriguing possibility led us to this story.
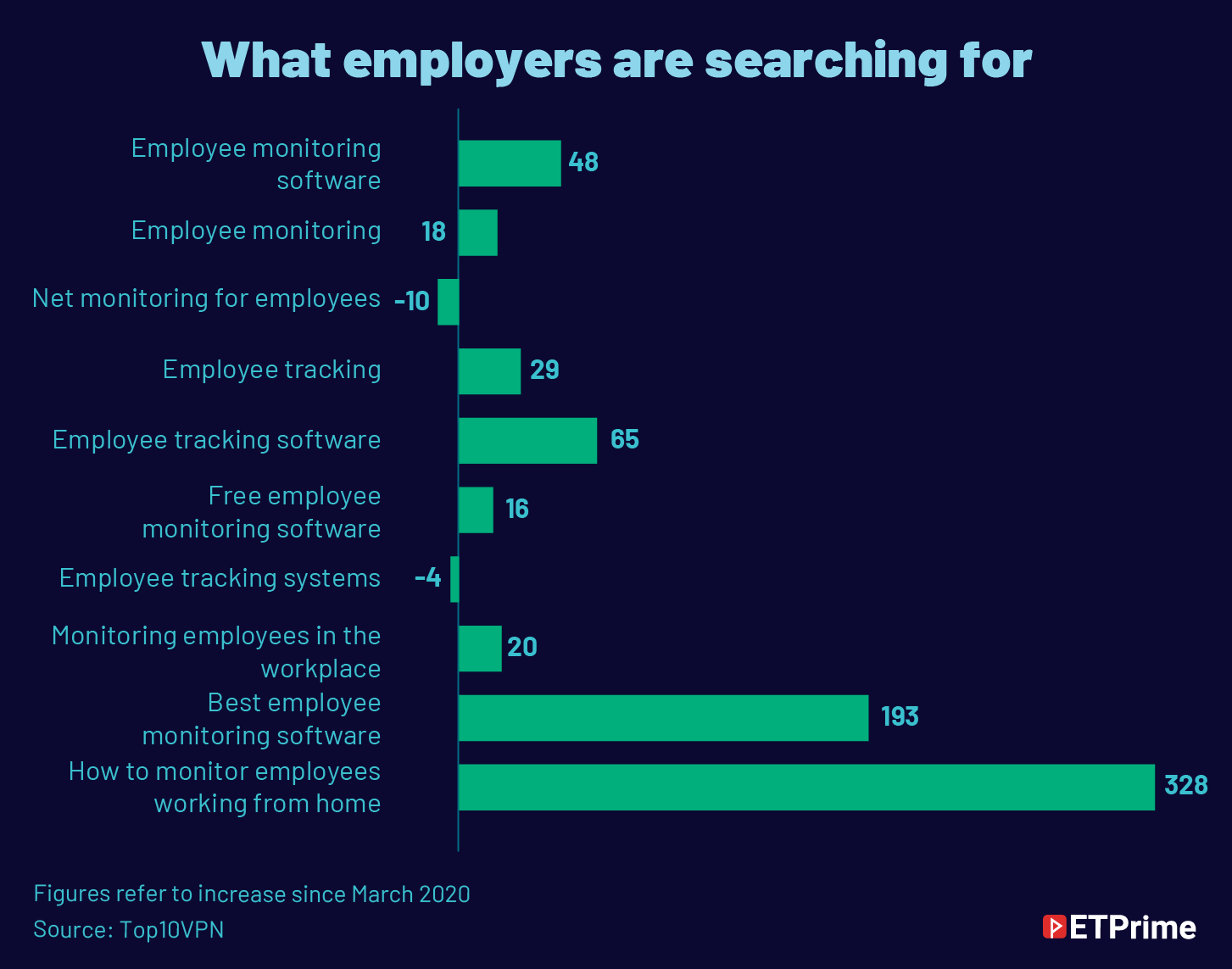
A casual Google search for employee surveillance software led us down the rabbit hole of the rise and rise of snooping by companies.
There are many changes that the pandemic has brought to the way we work. Perhaps, among the less known is the sheer extent to which employers have sought to track employees as they work from home.
Companies have been busy adding capabilities to a rich arsenal that already had keystroke recording, scraping of emails, monitoring of social media, tracking hardware, and data aggregation. As monitoring productivity and protection of customer data have become a top priority for companies, the demand for employee surveillance software has been on a steady rise.
The evidence is this: India is ranked behind only the United States with respect to Google searches for “employee monitoring”.
Impact of the new work culture
Before the pandemic, employees were connected to the Internet through the internal networks of companies and employers could monitor traffic and control access to websites such as YouTube or Netflix. But since employees are directly connected to the Internet under remote working, these capabilities had to be augmented.
This is especially important in the case of hardware that is issued by companies. While the practice of BYOD (bring your own device) has been on the rise, the device ecosystem, particularly when it comes to laptops, is dominated by company-issued hardware.
According to Mark Walker, security solutions lead at Jamf, an enterprise-management software provider that specialises in Apple’s ecosystem, over the last couple of years many organisations have been struggling to secure and monitor connectivity as well as how employees use hardware.
This is because hardware usage pattern has changed dramatically. With employees’ work and personal lives converging, devices are increasingly being used for personal purposes. From the point of view of companies’ chief information security officers (CISOs), this raises major concerns.
For instance, man-in-the- middle attacks (when communication between two systems or people is intercepted by an unauthorised party) can result in serious data breaches. In the era of ransomware, it can result in problems rapidly spreading across a company’s network. There are serious cybersecurity risks that could lead to companies losing control in the absence of a unique vantage point.
Therefore, in this context, an overview of how employees work from home becomes imperative for CISOs. And employee-surveillance software makers help them do exactly that.
Trust deficit and demand spike
According to Top10VPN, a company that reviews and publishes research to protect online privacy and security, demand for employee-surveillance software globally has recorded a massive 54% jump since early last year when the pandemic hit. Hubstaff, Time Doctor, and FlexiSPY are among the most popular software used by companies for employee surveillance.
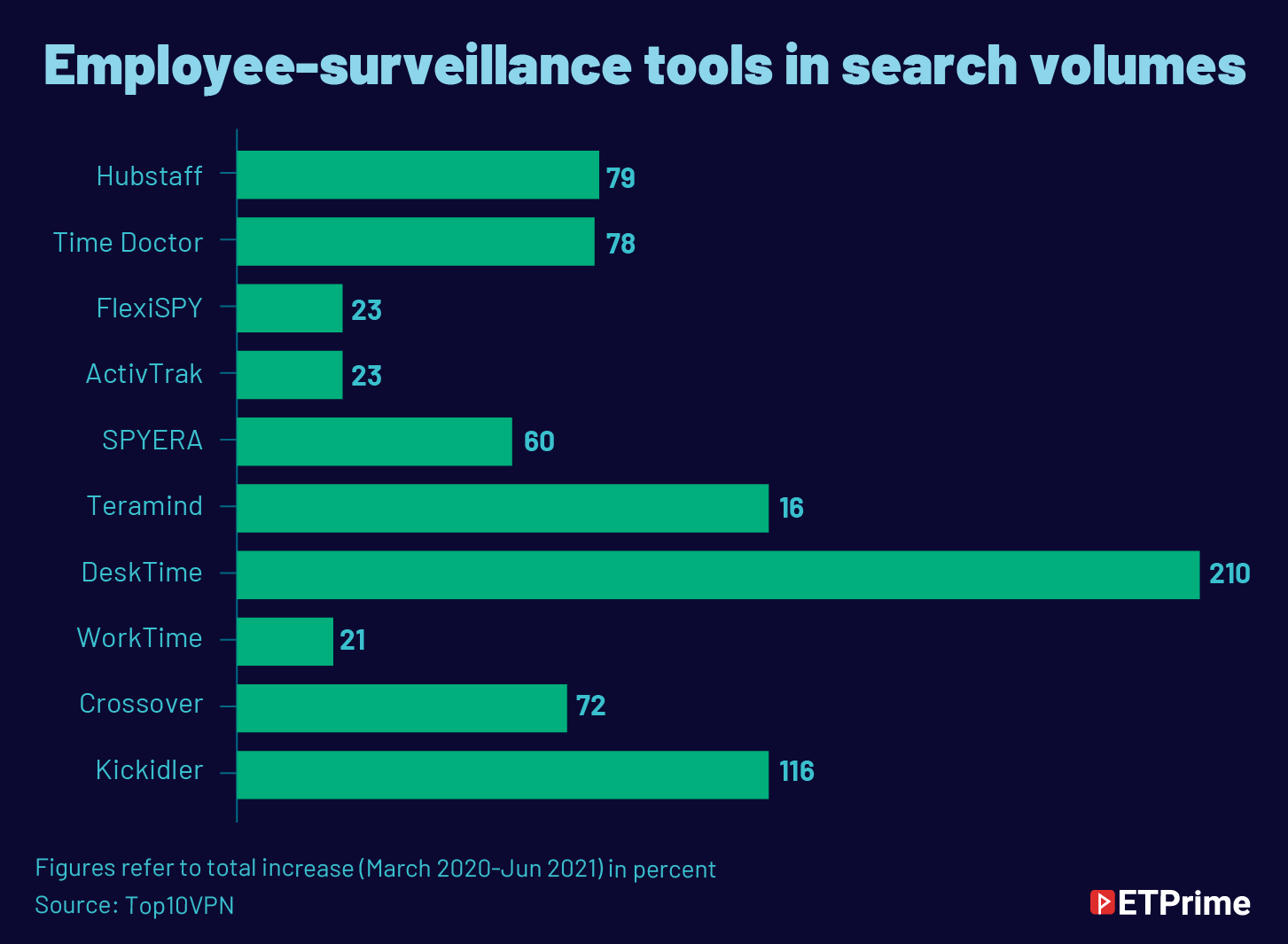
Eli Sutton, vice-president of global operations, Teramind, a company that makes software that helps employers monitor productivity, says that the company has enjoyed 3x the usual business since the start of the pandemic. “Our software fulfils both productivity and security requirements for any organisation looking to employ a remote workforce. To further clarify, Teramind can report on user activity with the end goal of optimising workforce productivity. On the flip side, it also provides security to the endpoint being used with the end goal of mitigating the insider threat (whether malicious or indirect),” he adds.
Simon Migliano, head of research, Top10VPN, says, “The corporate world is still getting to grips with remote working as a genuinely legitimate and positive concept that can benefit employers as well as staff. The data shows that too many employers don’t trust their teams to be productive working from home without strict surveillance”.
He adds that employee surveillance software reassures employers that their employees are not slacking off work by giving them access to data on team members’ keystrokes and the time spent in front of their screens.

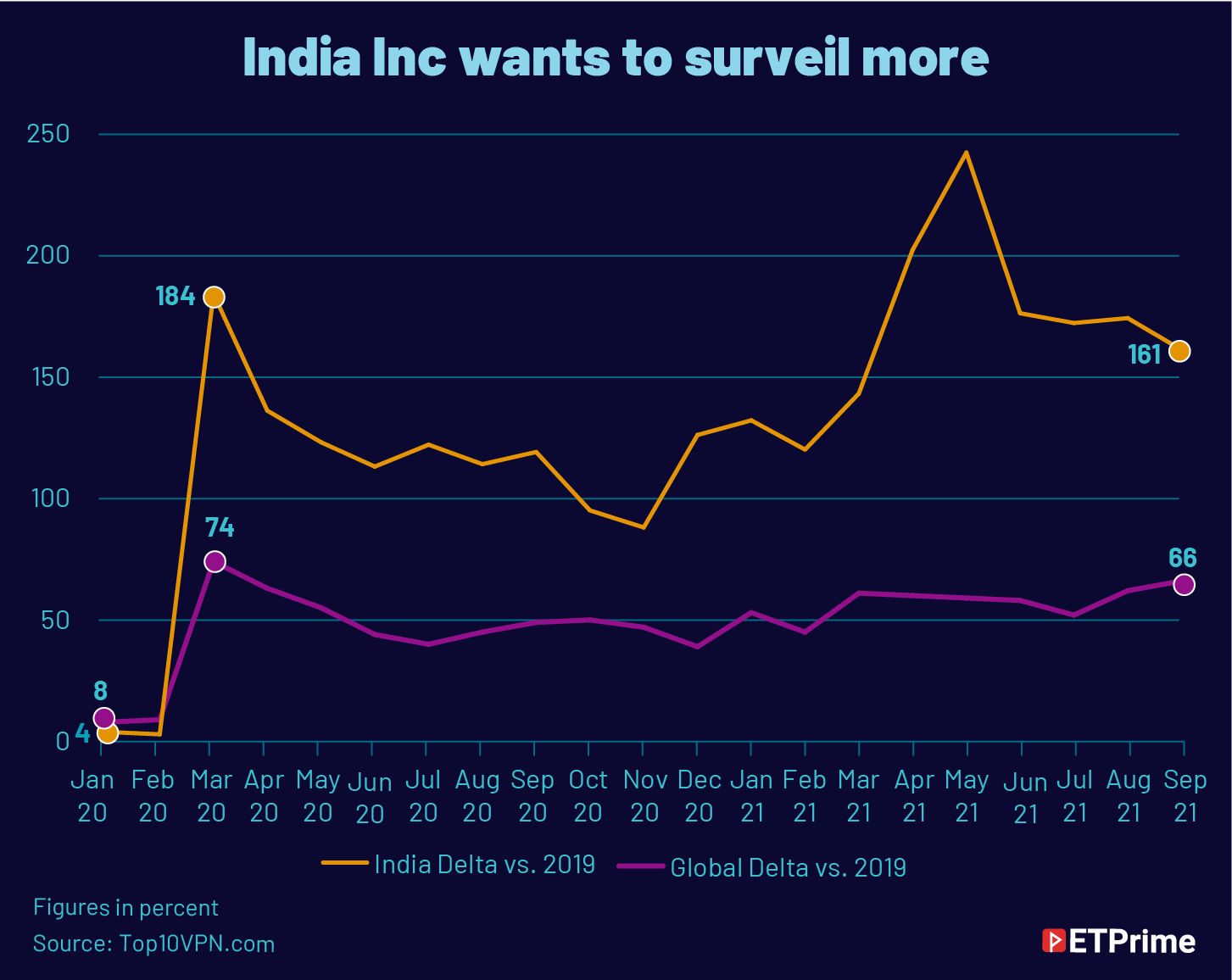
In tune with the rest of the world, India, too, has seen an increase in demand for such software. However, the biggest surge in demand was witnessed between the months of March and June in 2020 and 2021. This could be attributed to the shift to remote working amid the two waves of the pandemic.
But that does not explain why the country witnessed a spike in these months in both the years even as the global demand remained relatively constant.
Perhaps IT admins and CISOs in the country are taking to such software at a faster pace since historically their penetration has been low.
Deep capabilities
While the debate on the extent of employee surveillance remains inconclusive, what is clear, however, is that such software have powerful capabilities. Teramind, for instance, according to Sutton “Can report on a variety of user actions. These include websites and applications, emails, keystrokes, social media, instant messengers, prints, searches, console commands, file transfers, screen snapshots, and online meetings.
Some allow admin to remotely take control of webcams and microphones, which should ring alarm bells as it amounts to an intrusion of privacy. This is not even taking into account the fact that such software have keyloggers, or the capability to capture every keystroke including passwords, which can then be viewed by the admin in case they wish to.
In real time, this could give admin the capability to track specific keywords, which when typed in can alert them. On top of this, makers of such software are also adding features such as ‘content analysis and content filtering’. There are also features that help admin to take complete control without the knowledge of employees.
Keylogging should raise a red flag for employees using company hardware for personal purposes such as net banking and credit card transactions. But while companies may be using them extensively, most employees aren’t aware of the sheer muscle of such software. That is because these are generally installed by admin as ‘updates’.

Explaining how Teramind’s software works, Sutton says, “It’s an agent-based solution that needs to be installed on the endpoint that requires monitoring. From there, it can provide screen recording, report on user actions, and intervene in those actions when necessary”.
It operates in two modes — Revealed and Stealth. In the former, “The user in question has full knowledge they are being monitored and can even interact with the agent (enable and disable based on their task assignments). The Revealed agent has been widely adopted as many users who work remotely are using their personal devices. This allows the user to disable the agent if they are doing something private (like logging into a health or banking portal)”.
According to Sutton, the Stealth agent runs once the user logs in and an admin can specify hours for which the agent runs. “The user in question does not have the ability to interact with the Stealth agent. It is typically used when monitoring with the end goal of mitigating the insider threat.”
There is also a lot of room for flexibility in these software. “An admin can specify which reports are necessary for which users or departments. You do not have to monitor each user at full blast, and [can] rather monitor for what’s necessary. Furthermore, Teramind comes with a built-in policy enforcement engine that can alert an admin or the user when a policy is violated. It can request confirmation before committing certain user acts or block them altogether. It can go as far as locking the user out of their endpoint if what they are doing can cause serious harm to the organisation,” Sutton adds.
Of course, the safest thing for employees is to not use corporate hardware for personal work on. But the reality is that the capabilities of such software go even beyond that and includes intrusive features like switching on webcams or microphones.
“The corporate world is still getting to grips with remote working as a genuinely legitimate and positive concept that can benefit employers as well as staff. The data shows that too many employers don’t trust their teams to be productive working from home without strict surveillance.”
— Simon Migliano, head of research, Top10VPNPrivacy vs. security
Indeed, companies do have valid reasons to augment data protection as any breach amounts to business risk. As Migliano puts it, “Typically, employee-surveillance software will be installed on corporate devices and their use will be contractually required. As the use of these devices is for work purposes, it is legal to monitor employees on the grounds of ensuring data security and that the employee is fulfilling the obligations of their employment contract”.
While that is legally sound, companies should ideally inform employees of the capabilities of the software that they are taking home. “While employee surveillance is legal and the technology exists to monitor employees’ every move, employers using such software should stop and think about the ethics of doing so and its corrosive effect on team morale and culture,” Migliano adds.
Data privacy is the cornerstone of technology across geographies. Regulatory interventions such as General Data Protection Regulation mean that storing and processing any data that could be deemed personal will require consent. In case companies gather non-work related data, for instance, by switching on a webcam or the microphone, they could land in trouble.
Indeed, it is a complex issue that requires more conversation.
(Graphics by Manali Ghosh)
The latest from ET Prime is now on Telegram. To subscribe to our Telegram newsletter click here.